Home
Recommended
Other Links
Cisco Talos’ Vulnerability Discovery & Research team recently disclosed one Foxit Reader vulnerability, and six LibRaw file reader vulnerabilities.
The vulnerabilities mentioned in this blog post have been patched by their respective vendors, all in adherence to Cisco’s third-party vulnerability disclosure policy.
For Snort coverage that can detect the exploitation of these vulnerabilities, download the latest rule sets from Snort.org, and our latest Vulnerability Advisories are always pos
Learn to find and exploit real-world agentic AI vulnerabilities through five progressive challenges in this free, open source game that over 10,000 developers have already used to sharpen their security skills.
On April 13, 2026 at 03:55:23 UTC, a helper contract deployed by the attacker used Hyperbridge's Ethereum-side ISMP message path to deliver a forged governance-style `PostRequest` into `TokenGateway`. The exploit is best classified as an access-control failure at the proof-validation boundary: `Hand...
Multi-agent pipeline for on-chain attack analysis with Analyst-Validator debate loop
7-stage orchestrated audit for blockchain node codebases (Go, Rust, C/C++)
DFS-based multi-agent Solidity audit with adversarial validation
On April 12, 2026, SubQuery Network, a staking protocol on Base, (block 44,590,469) suffered an access-control exploit that drained approximately **218.29M SQT** (about **$131.2K**) from the protocol's Staking contract. The attacker deployed two ephemeral contracts, abused the absence of any owner o...
"A few months ago I had this realization that agents have become really good at identifying bugs in code, especially security vulnerabilities. They are …"
CVE-2026-24450
An integer overflow vulnerability exists in the uncompressed\_fp\_dng\_load\_raw functionality of LibRaw Commit 8dc68e2. A specially crafted malicious file can lead to a heap buffer overflow. An attacker can provide a malicious file to trigger this vulnerability.
The versions below...
CVE-2026-20911
A heap-based buffer overflow vulnerability exists in the HuffTable::initval functionality of LibRaw Commit 0b56545 and Commit d20315b. A specially crafted malicious file can lead to a heap buffer overflow. An attacker can provide a malicious file to trigger this vulnerability.
The...
CVE-2026-24660
A heap-based buffer overflow vulnerability exists in the x3f\_load\_huffman functionality of LibRaw Commit d20315b. A specially crafted malicious file can lead to a heap buffer overflow. An attacker can provide a malicious file to trigger this vulnerability.
The versions below were...
<div class="h2"><span id="challenge-error-text">Enable JavaScript and cookies to...
On April 5, 2026, Denaria Finance, a perpetual DEX on Linea, (block 30,067,821) suffered a virtual AMM manipulation attack that drained approximately **165,618 USDC** from the protocol's Vault. The attacker flash-loaned 60,000 USDC from Aave V3, deployed pairs of ephemeral LP and Trader contracts, a...
A recent article of the OpenBSD journal caught me attention: Pledge changes in 7.9-beta (archive.org mirror as it's currently offline).
The quoted message starts with:
> Previously under certain promises it was possible to open certain files or devices even if the program didn't pledge "rpath" or...
If you squint and look at the CISA KEV list, you might think it's made up exclusively of vulnerabilities in file transfer solutions.
While this would be wrong (and you shouldn’t squint, it’s bad for your eyes), file transfer solutions do play a decent role in the CISA KEV list due to how fondly threat actors, APT groups, and ransomware gangs alike perceive them.
The following represent industry-defining historical incidents:
* The MOVEit breach in 2023,
* Cleo Harmony, VLTrader and LexiCom
The purpose of the BitLocker check I implemented in PrivescCheck is to determine whether the system drive is protected, and if so, whether two-factor authentication is configured (typically TPM+PIN). You’d think that it’s a simple thing to do, but it is not, at least without administrator rights.
Recent attacks on open source focus on exfiltrating secrets; here are the prevention steps you can take today, plus a look at the security capabilities GitHub is working on.
TL;DR In January 2026, the Chrome Releases blog announced several security fixes across different Chrome components. One entry caught our attention: CVE-2026-0899, an Out-of-Bounds memory access in V8 discovered by @p1nky4745.
Vulnerabilities in V8, especially OOB and Type Confusions are always interesting from a security research perspective. We decided to take a closer look. At the time of writing, the issue was still restricted and no public proof-of-concept was available. After reverse engineering the patch fix, we identified the root cause of the vulnerability and developed a trigger PoC.
Key Points Introduction At the beginning of 2026, Check Point Research observed a series of targeted attacks against government entities in Southeast Asia carried out via a legitimate TrueConf software installed in the targets’ environment. The investigation led to the discovery of a zero-day vulnerability in the TrueConf client, tracked as CVE-2026-3502 with a CVSS score of 7.8. […]
CVE-2026-3779
A use-after-free vulnerability exists in the way Foxit Reader handles an Array object. A specially crafted JavaScript code inside a malicious PDF document can trigger this vulnerability, which can lead to memory corruption and result in arbitrary code execution. An attacker needs to...
On March 31, 2026 at 22:56:21 UTC (Polygon block `84938872`), an attacker exploited WhaleBit's unverified staking system through a **same-transaction spot-oracle manipulation** funded by a flash loan. The attacker EOA `0xe66b37de57b65691b9f4ac48de2c2b7be53c5c6f` used helper contract `0xb5a8d7a37d60a...
On March 31, 2026 at 20:39:02 UTC, the attacker used flash-loaned capital on BNB Chain to manipulate the LML/USDT market, then batch-triggered reward claims for pre-seeded accounts through APower and immediately sold the resulting LML back into the distorted pool. The primary issue is a price-manipu...
Two compounding flaws in InfinitySix's (`$i6`) BSC staking contract were chained to extract **273,802 USDT** in block 89,703,286. The contract credits referral bonuses to a sponsor's withdrawable balance immediately upon the referral's `invest()` call; separately, its TWAP oracle enforces a 1-minute...
# OpenOlat - RCE via Server-side Template Injection (SSTI) and OIDC Auth Bypass
## Summary
We identified an exploitable SSTI within OpenOlat that allowed for code execution on the host for authenticated users with authoring permissions. Additionally, an authentication bypass in the OIDC implicit...
Key Takeaways What Happened AI assistants now handle some of the most sensitive data people own. Users discuss symptoms and medical history. They ask questions about taxes, debts, and personal finances, upload PDFs, contracts, lab results, and identity-rich documents that contain names, addresses, account details, and private records. That trust depends on a simple expectation: […]
Today, we woke up with a nagging feeling: what if Citrix had, in fact, patched multiple Memory Overread vulnerabilities as part of CVE-2026-3055?
While we've been using our analysis from Part 1 (please read it first, as this post will be brief) to accurately identify exploitable Citrix NetScaler appliances across the watchTowr client base, we couldn't help but wonder: could there be more hiding in Citrix's patches?
These thoughts, and worse, naturally come to us at 6 am on a Sunday morning.
W
KEY FINDINGS AI-assisted malware development has reached operational maturity.VoidLink framework, which is modular, professionally engineered, and fully functional,was built by a single developer using a commercial AI-powered IDE within a compressedtimeframe. AI-assisted development is no longer experimental but produces deploymentreadyoutput. AI-assisted development is not always obvious from the final product.VoidLink was initially assessed as the […]
Sequels? Pain? We're obviously talking about Citrix NetScalers, yet again.
Welcome back to another watchTowr Labs blog post - pull up a chair, we always welcome new members to our group therapy sessions.
If you asked a C programmer what they most dislike doing in life, their answer might well be:
* Using an IDE,
* Constantly rejecting job offers to work on Citrix NetScalers,
* Wishing they could go back to Assembly, and,
* Writing string processing code.
While C is to some a glorious and
On 2026-03-28, the VTSwapHook contract (`0xbf4b4a83708474528a93c123f817e7f2a0637a88`) deployed on Arbitrum was exploited through a **logic error** in its custom pricing formula. The hook implements a nonlinear (logarithm-based) price curve but approximates execution price using a simple midpoint ave...
# A Technical Deep Dive into CVE-2024-23380: Exploiting GPU Memory Corruption to Android Root
# Table of Contents
In our last blog, we talked about Binder exploit and fuzzing, and how they can be used to achieve Local Privilege Escalation (LPE) from a zero-permission application to root. In this...
On 2026-03-27, the EST / BNBDeposit system on BNB Smart Chain was exploited through a **flash-loan-assisted reward-accounting flaw** in `BNBDeposit`, amplified by **fee-exempt routing and pair-state manipulation** in EST. The attacker borrowed `250,000 WBNB`, built a temporary claim-bearing share in...
Cisco Talos’ Vulnerability Discovery & Research team recently disclosed a vulnerability in HikVision, as well as 10 in TP-Link, and 19 in Canva.
The vulnerabilities mentioned in this blog post have been patched by their respective vendors, all in adherence to Cisco’s third-party vulnerability disclosure policy.
For Snort coverage that can detect the exploitation of these vulnerabilities, download the latest rule sets from Snort.org, and our latest Vulnerability Advisories are always posted on
Reviewed advisories hit a four-year low, malware advisories surged, and CNA publishing grew—here’s what changed and what it means for your triage and response.
Overview This post explores how modifying a Dell UEFI firmware image at the flash level can fundamentally undermine platform security without leaving visible traces in the firmware interface. By directly...
Kubernetes forensics 1/3 : what the container ?
The mysterious unreadable `kernseal.txt` file on PaX' documentation
page has been sitting there since
2003, described as "sealed kernel storage design & implementation." In 2006, it
was described
as:
> the problem KERNSEAL sets out to solve is kernel self-protection, that is, assuming arbitrary...
Reported to: Salesforce
Product: Workbench
Date Reported: 2026-03-23
Severity: Redacted until the 90-day disclosure is lifted.
90-day Deadline Expires: 2026-06-21
Despite recent advancements in adoption of passkeys, passwords remain one of the most widely used authentication mechanisms on the web, yet repeated studies have demonstrated that humans are particularly bad at generating them. Chromium (the open-source project that Edge and Chrome are based upon) uses a library called “zxcvbn” created by Dropbox to perform strength estimation, and you may have seen a dialog box such as this while creating login credentials in Edge [figure 1]. FIGURE 1: PASSWORD STRENGTH & SUGGESTION DIALOG
A high impact bug sometimes needs just one small additional detail before it turns into a practical attack vector. For that reason, when doing vulnerability research, I flag even errors or odd behaviors that look irrelevant at first. In some cases, those findings become the missing puzzle piece of a high-impact vulnerability. In this article, […]
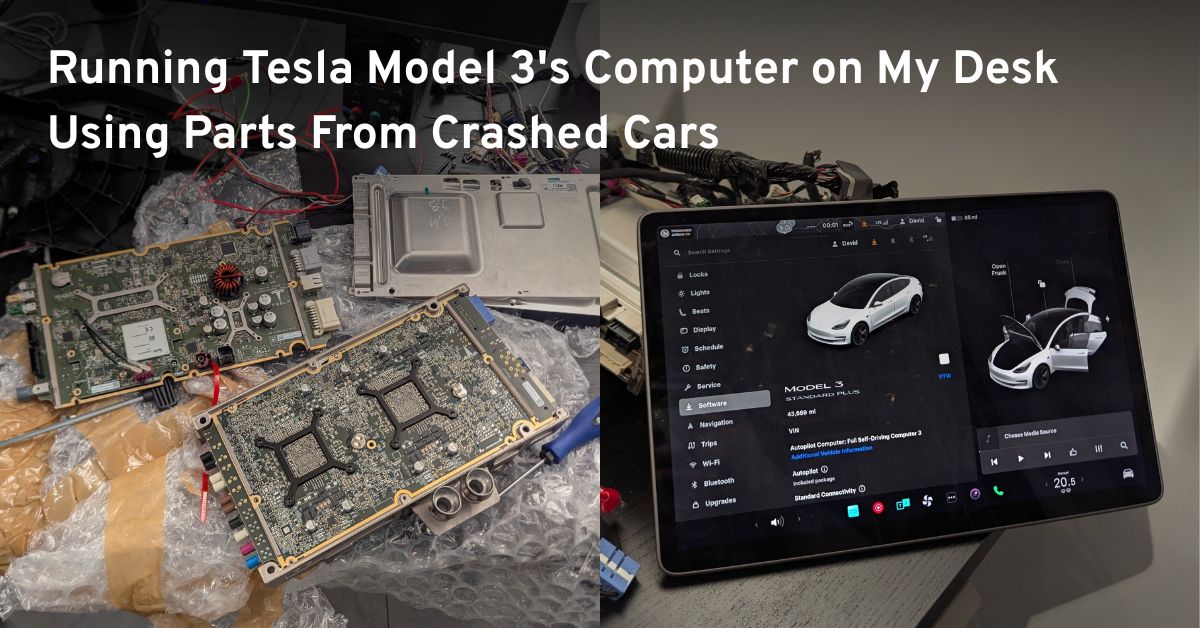
Tesla runs a bug bounty program that invites researchers to find security vulnerabilities in their vehicles. To participate, I needed the actual hardware, so I started looking for Tesla Model 3 parts on eBay. My goal was to get a Tesla car computer and touchscreen running on my desk, booting the...
Exploring cross-domain & cross-forest RBCD
Tesla runs a bug bounty program that invites researchers to find security vulnerabilities in their vehicles. To participate, I needed the actual hardware, so I started looking for Tesla Model 3 parts on eBay. My goal was to get a Tesla car computer and touchscreen running on my desk, booting the...
An unverified escrow-like contract at `0xf0a105d93eec8781e15222ad754fcf1264568c97` on Ethereum Mainnet was fully drained in block 24,707,679 (timestamp 2026-03-22 UTC) through an **integer overflow** in its deposit function `0x317de4f6`. The deposit function accumulates entry amounts into a running ...
On March 22, 2026, the CyrusTreasury protocol on BNB Chain was exploited through a price manipulation attack against its `withdrawUSDTFromAny` function, which is called internally by `exit()`. The vulnerable contract (`CyrusTreasury`, `0xb042ea7b35826e6e537a63bb9fc9fb06b50ae10b`) reads the live Panc...
This vulnerability was such a gaping hole in the Windows Error Reporting service that Microsoft completely removed the affected feature. A low privilege user could simply send a specially crafted ALPC message with a reference to a command line that the service executed with SYSTEM privileges. At least that’s what I thought initially.
A long, long time ago, in a land free of binary exploit mitigations, when Unix still roamed the Earth, there lived a pre-authentication Telnetd vulnerability.
In fact, this vulnerability was born so long ago (way back in 1994) that it may even be older than you. To put the timespan in perspective: it came into existence the same year the seminal movie Hackers was released.
That was so long ago that RISC was still a distant dream.
Come to think of it, maybe it was even the product of Zero Cool
Deep-dive into the deployment of an on-premise low-privileged LLM
SolarWinds. Ivanti. SysAid. ManageEngine. Giants of the KEV world, all of whom have ITSM side-projects.
ITSMs, as a group of solutions, have played pivotal roles in numerous ransomware gang campaigns - not only do they represent code running on a system, but they hold a significant amount of sensitive information. With the ability to track IT inventory, configuration files, and incident reports, threat actor campaigns have never been so organized.
BMC FootPrints last received a CVE in 2014. To
CVE-2025-66176
A stack-based buffer overflow vulnerability exists in the SADP XML parsing functionality of Hangzhou Hikvision Digital Technology Co., Ltd. Ultra Face Recognition Terminal 3.7.60\_250613 and Face Recognition Terminal for Turnstyle 3.7.0\_240524 (under emulation). A specially crafted...
On 2026-03-18, the dTRINITY dLEND lending protocol (an Aave v3 fork deployed on Ethereum mainnet) was exploited through a **flash loan abuse combined with a logic error** in the flash loan repayment accounting. An attacker manipulated the cbBTC reserve's liquidity index from ~1.0 RAY to 6,226,622 RA...